Google’s cybersecurity experts have uncovered evidence suggesting that hackers, believed to be sponsored by the governments of Russia and China, have been taking advantage of a previously identified weakness in WinRAR, a widely used Windows file compression tool.
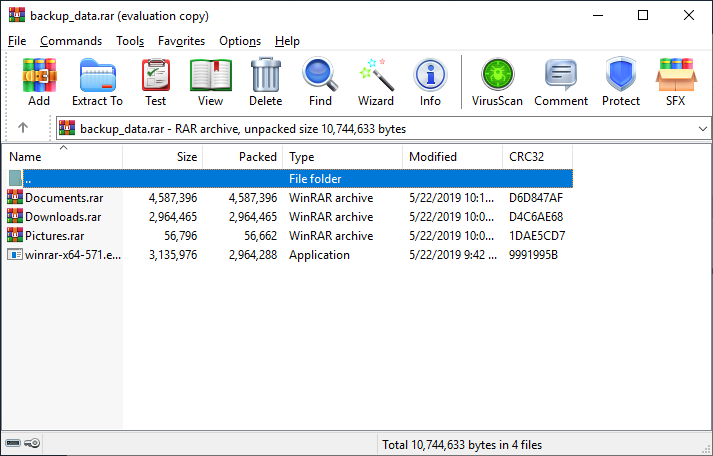
The vulnerability in question was initially pinpointed by cybersecurity firm Group-IB earlier this year and is recognized as CVE-2023-38831. It lets perpetrators embed harmful code within archive files that outwardly appear to be regular images or textual files. According to Group-IB, this vulnerability had been actively exploited since April, even before a fix was available — a scenario often termed as a “zero-day” exploit. By leveraging this vulnerability, adversaries managed to breach at least 130 trading systems.
Rarlab, the developers behind WinRAR, responded by rolling out a fixed version (WinRAR 6.23) on August 2.
Yet, Google’s Threat Analysis Group (TAG) reports that despite the fix, multiple state-affiliated hacking entities are still exploiting this vulnerability, primarily targeting users who have not yet updated their software. Their in-depth research, shared with TechCrunch, suggests that these exploits can be attributed to hacking syndicates associated with the governments of Russia and China.
Among the implicated parties is Sandworm, a notorious hacking group connected to Russian military intelligence. Sandworm has been previously implicated in major cyberattacks, such as the devastating NotPetya ransomware attack in 2017 which severely impacted Ukraine. TAG’s analysis suggests that in September, Sandworm misused the WinRAR vulnerability in a malicious email campaign, posing as a Ukrainian drone warfare training institution.
Another well-known Russian-affiliated hacking entity, Fancy Bear (or APT28), is also reported to have used the WinRAR exploit, targeting Ukrainian entities with deceptive emails seemingly sent by the Razumkov Centre, a Ukrainian public policy institute. Fancy Bear gained international infamy following their 2016 attack on the Democratic National Committee.
Further insights by Cluster25, a threat intelligence firm, echo these findings, having observed similar exploitation tactics traced back to Russia. Their assessment suspects Fancy Bear to be the main orchestrator.
Furthermore, Google’s experts have identified another cyber espionage group, APT40, believed to be backed by the Chinese state, as an abuser of the same WinRAR flaw. This group reportedly targeted individuals in Papua New Guinea via phishing campaigns carrying the CVE-2023-38831 exploit.
In light of these revelations, TAG emphasizes the significance of timely software updates, highlighting that even after vulnerabilities are known and patched, they can still be potent weapons in a hacker’s arsenal due to delayed user updates.